UpSight fortifies endpoints at the kernel level by integrating deep within the operating system to monitor and control system activity with unparalleled precision. This approach enables proactive defense by intercepting malicious behavior—such as unauthorized encryption, privilege escalation, or process injection—before it can impact critical systems. By operating below the application layer, UpSight prevents threats in real time, without relying on signatures or post-breach detection.
End Ransom Operations with Security
Purpose Built to Solve the Problem
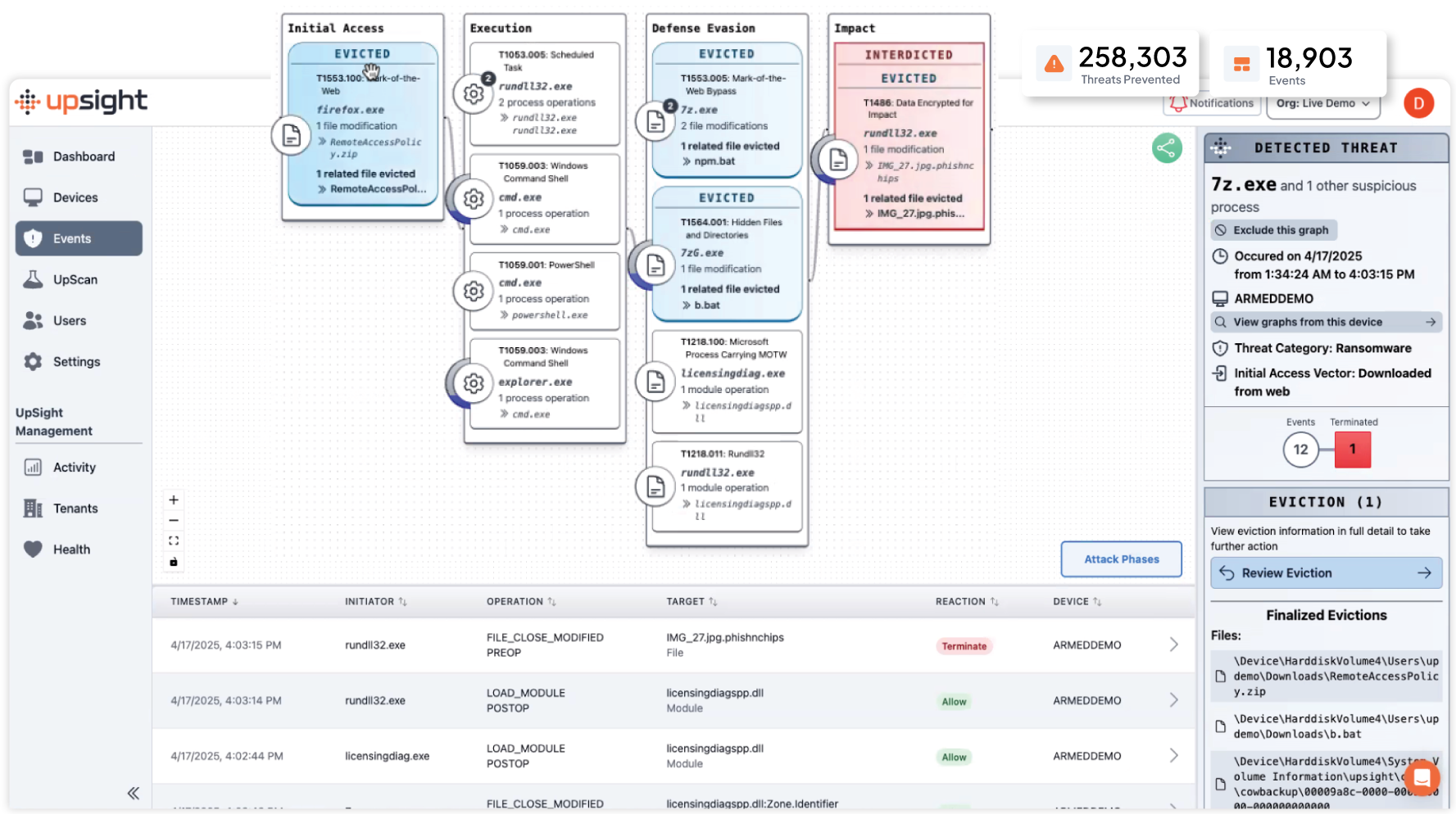
The UpSight platform was created to disrupt the ransom operation and eliminate the cost to recover by leveraging advanced AI and innovative endpoint design to deliver real-time prediction, prevention, and recovery.
Complete Ransomware Protection
Requires an Innovative Approach
Our patented approach leverages AI and ML techniques to translate machine language into a unique natural language sentence structure aligned to MITRE ATT&CK to predict what will happen next in a sequence of activity.

Fortify Endpoints at the Kernel Level
This deep visibility and control set the foundation for Interdict, our advanced threat prevention engine, which intelligently identifies and neutralizes ransomware activity at the moment of execution—stopping attacks before they start.

Make Ransoms economically unviable
UpSight disrupts the ransomware economy by neutralizing attacks before they can encrypt or exfiltrate valuable data. By operating at the kernel level with real-time prevention, UpSight stops ransomware in its earliest stages—before any ransom demands or operational disruptions can occur. This eliminates the attackers’ ability to profit, removing the financial incentive that drives ransomware operations.
-
Immediate Threat Interdiction: Malware and ransomware processes are stopped mid-execution, preventing encryption, data theft, or lateral movement.
-
No Opportunity for Ransom: Without successful encryption or extortion leverage, attackers cannot demand payment.
-
Cost Reduction for Defenders: By preventing successful attacks, organizations avoid ransom payments, downtime, recovery costs, and reputational damage.
-
Breaking the Ransomware Business Model: As attack success rates drop and profitability diminishes, ransomware groups are deterred from targeting protected organizations.
-
Strategic, System-Level Defense: Unlike reactive solutions that detect ransomware post-breach, UpSight’s preemptive kernel-layer protection rewrites the economics of ransomware entirely.

Endpoints become resilient to ransom operations without the need for remediation and recovery.
With UpSight.ai, endpoints don’t just detect ransomware—they become inherently resilient to it. By embedding protection at the kernel level, UpSight.ai intercepts malicious actions before they can encrypt files, steal data, or escalate privileges. Ransomware operations are neutralized in real time, stopping attacks before any damage occurs.
This proactive defense model eliminates the traditional need for costly remediation, lengthy forensic investigations, and complex recovery processes. Systems stay operational, data stays intact, and businesses avoid downtime or ransom payments altogether.
By hardening endpoints with UpSight.ai, organizations move from a reactive posture to a resilient one—where ransomware threats are simply rendered ineffective.
Unlock the advantages of UpSight AI
Prevent Downtime
Preventing downtime is crucial for maintaining seamless system operations and ensuring continuous business productivity. By keeping your systems running without interruption, your organization can avoid costly outages that disrupt workflows and lead to financial losses. A reliable and resilient infrastructure ensures that your operations remain online, maximizing efficiency and keeping your team productive without unexpected disruptions.
Avoid Costly Outages
Eliminating ransom operations is essential in the fight against cyber extortion and ransomware threats. By implementing strong security measures, businesses can stop ransomware in its tracks and prevent attackers from holding critical data hostage. A proactive defense strategy ensures that your organization is protected from cyber threats, eliminating the risk of costly breaches and operational paralysis caused by malicious actors.
Recover Instantly and Permanently
Recovering instantly and permanently is key to maintaining business continuity in the face of disruptions. With rapid, lasting recovery solutions, businesses can restore lost data within seconds, minimizing downtime and ensuring resilience. Secure and instant data restoration guarantees that valuable information is never lost, allowing organizations to stay operational and maintain confidence in their recovery capabilities.
UpSight Console Information
Minimial Impact,
Powerful Performance
UpSight’s thin client SLM monitors billions of endpoint events directly on the device, continuously analyzing system activity without compromising performance.
Minimal Resource Impact
Overlay Security Compatible
Advanced Agent Capabilities
UpScan Testing Environment
UpSight Features & Benefits
UpSight Security delivers not just resilience but true confidence in the face of ransomware.
Prevent Ransomware
Prevent Financial & Reputational Damage – Mitigate extortion risks, revenue loss, and brand damage caused by ransomware attacks.
EDR/EPP Enhancement
Enhance Resiliency & Confidence – Strengthen prevention strategies and ensure safe ransomware eviction without compromise.
Instantly Restore Endpoints
Avoid Costly Backups & Downtime – Eliminate reliance on traditional backup restoration services and prevent business disruptions.
Reduce Data Costs
Lower Data Storage Costs – Reduce dependency on expensive data lakes by minimizing the need for excessive telemetry storage.
Reduce Alert Fatigue
Sorting through all the false positives is costly and ineffective for your IT and Security Ops. Our solution identifies the true positives for ransomware.
Quick Deployment
Works complimentary to your existing security stack with efficient deployment for specific and bulk device installation.






